The World Health Organization (WHO), on January 30th, 2020, declared COVID-19 a health emergency. The pandemic went ahead to revolutionize all sectors of human lives. Working environments changed from on-premises to remote working solutions.
A few months after the pandemic, remote working became the new normal. A Gartner survey indicates that 88% of organizations across the globe made it mandatory for their employees to work from home after the pandemic.
But remote working came with its share of challenges. Cybersecurity attacks targeting staff working remotely surged, causing fear and apprehension.
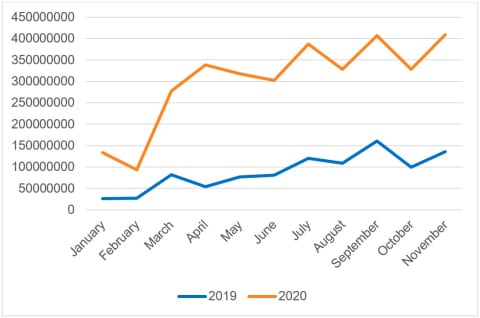
According to a Kaspersky report, there was an average of 3.3 billion attacks targeting remote working desktops. The figure represents a 242% increase since 2019.
As per Upwork’s Future WorkForce Pulse Report, 36.2 million Americans are projected to work remotely by 2025. This figure represents an 87% increase from the pre-pandemic period. It means that remote-working-related cybersecurity threats will continue to exist as long as the remote-working landscape exists. In this article, you will learn about some of the most effective cybersecurity tips for securing remote access for employees.
1. Craft a Clear and Elaborate Remote-Work Cybersecurity Policy
The first step to winning the war against hackers targeting your staff working remotely is setting up clear rules, policies, and guidelines that govern the remote working landscape.
Your remote staff could quickly become the entry point for a cyber attacker to infiltrate your networks and steal your data without clear guidelines.
Cybersecurity policies should encompass everything. For example, it should stipulate remote working security protocols. One of the critical aspects the policy should address is the case for company-owned devices vs. personal devices. Company devices tend to be much more secure than personal devices.
A Blurred Lines and Blindspots report reveals that 70% of remote workers tend to use their devices for office work. The same report also indicates that 30% of all the remote workers surveyed allow other parties to use their devices. In so doing, they jeopardize the entire organization by making it susceptible to hackers.
2. Data Encryption Tools
Data encryption is always an excellent strategy for any organization or business. But it should be given much weight when working remotely. Simply defined, encryption refers to the act of transforming plaintext data or information into a meaningless format referred to as ciphertext. Only the intended recipient who holds a cipher or an encryption key can read the data.
Encryption software and protocols such as SSL certificates will immensely boost the security of your remote data. Installing the certificate on remote working applications and websites is crucial because it will conceal the in-transit data making it indecipherable.
As a remote-working best practice, you must ensure that all your workforce operates on encrypted software. It is much easier to acquire a cost-effective SSL certificate for websites.
The reason is the Wildcard SSL certificate option, which allows users to use only one certificate on multiple first-level subdomains under the chosen main domain for their website. Wildcard certificates that you can choose for your remote working tasks include Comodo Positive SSL Wildcard, RapidSSL Wildcard SSL, and GeoTrust True Business ID Wildcard.
3. Employ A Virtual Private Network
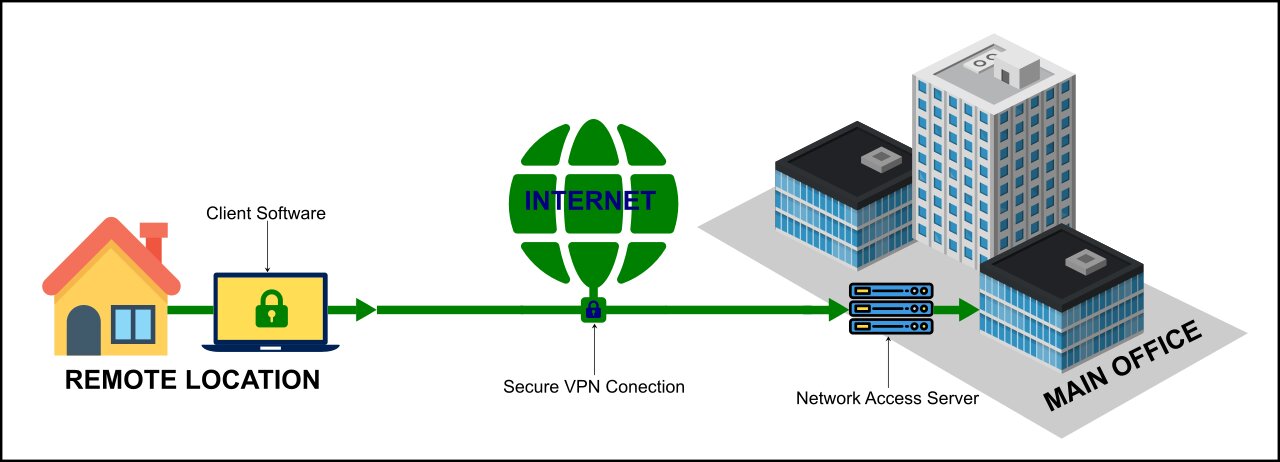
One of the most recommended cybersecurity tips for securing remote access for employees is by using a virtual private network. Simply put, A VPN is a software that helps create secure and encrypted internet connections. VPN uses tunneling protocols to encrypt data and communications between senders and receivers.
You should allow your remote staff to use a virtual private network when connecting to your organization’s internal networks as a best practice. In so doing, you will be saving your remote workers from the troubles caused by prying eyes and unauthorized intruders. There are several virtual private network services that you can employ.
4. Strong Passwords and Two-Factor Authentication
A recently released Verizon Data Breach Investigation Report shows that credentials compromises are the leading cause of 61% of organizations’ hacks. As such, password best practices are essential ingredients for every remote-working environment.
The first thing you should think about is having a strong and long password. Remote employees should be advised to secure their accounts by using passwords that are not less than eight characters in length. The passwords should also combine numbers, letters, and special characters/symbols.
Secondly, employees should be warned against reusing passwords. A Google/Harris Poll has indicated that 60% of people reuse passwords across multiple platforms. Reusing passwords jeopardizes remote work accounts. Using password manager tools is also a great way of securing your remote working environment.
But you should know that passwords alone can never provide the much-needed security for your authentication procedures. Hackers have proved that passwords are ineffective in the past, which is why you need to employ an extra authentication factor when signing into your remote work.
Two-factor authentication is vital because it makes it hard for attackers to access the second authentication factor. As a remote-work cybersecurity best practice, always ensure that you enable the multi-factor authentication feature.
5 Access Controls and the Least Privilege Principle
Another great way of securing your remote work environment is to limit worker privileges. There are three basic levels of access privileges which you should know of.
The first is the super-user level and comprises all team members with full access to network privileges. Such users have the power to install, modify, edit, set, and use system data. With all these powers come extreme repercussions if super-user accounts fall into the wrong hands.
The second level is the standard user level, which is popularly referred to as the least privileged user.
This user-level offers the most limited set of privileges, and it is the most recommended level for remote workers. Restrictions should apply to file editing and data views by your remote workers. Doing so will significantly eliminate the risk of data breaches.
6. Employee Cybersecurity Training and Awareness Program
Insider threats are now on the rise, and so are the cost of insider threats. A 2020 Cost of Insider Threats: Global published by the Penemon institute shows that the average cost of insider threats stands at $11.45 million.
Negligence should be blamed for such cases, and the only way to remove negligence is by having an employee training and awareness program.
The security training programming is essential because it will help equip employees with the best measures required to protect their remote work from security vulnerabilities.
A decent employee cybersecurity training and awareness program establishes a culture of security for your remote workers and helps to keep your environment more secure.
7. Collaborate With Third-Party Vendors
The remote-working environment requires adequate collaboration with your third-party vendors. Third-party vendors might include the company providing remote desktop access or managing file servers.
It would help if you only worked with vendors and partners committed to ensuring that your remote workforce is safe and secure from cybersecurity vulnerabilities.
Conclusion
If you have been contemplating having your employees work from their homes or you already have employees working from home, you must have adequate security protocols to protect them.
Failing to do so will jeopardize your remote workforce and your security at large. This article has explained some of the most notable measures you should have to secure your remote workforce.






Leave A Comment